How Easy Is It to Brute Force Your Password?
Passwords are viewed as your first line of defense against cyber criminals attempting to break into your organization.
While various other controls and tactics can be used to protect your applications, your password is often the most sought-after credential when cyber criminals want to steal your data. That being said how you create your password will determine how easy it is for criminals to either steal of guess it.
Hackers will often use "brute force" methods to try and gain access to your various applications and programs. This involves inputting large swaths of some of the most commonly used passphrase in order to simply get lucky and guess the correct one. Because so many people use short, personal or easy to remember passwords it oftentimes only takes a few minutes or even seconds for a hacker to brute force their way inside.
Passwords such as "1234" or "password" are commonly used passwords that cyber criminals could guess in an instant.
Here is a chart showing how long it takes criminals to brute force a password based on a variety of factors:
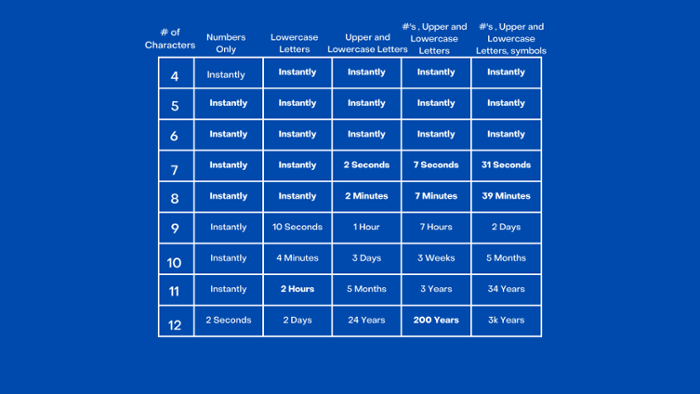
A 12-character password takes 62 trillion times longer to crack than a six-character password (Scientific American)
We see through this graphic that passwords made up of a few characters that only use numbers or lowercase letters can be guessed almost instantaneously. Passwords made up of 10 or more characters alongside a combination of numbers, lowercase, uppercase, and symbols are not so easily brute forced.
Establishing a secure password policy greatly improves your security posture and can protect all of your work applications. Your passwords should be complex, meaning they are 8 characters or greater, don't contain personal information, are changed regularly, and aren't repeated across applications.
CorpInfoTech can help you establish policies and procedures to protect your organization!
CorpInfoTech (Corporate Information Technologies) provides small to mid-market organizations with expert I.T. services including compliance assessment, cybersecurity penetration tests, and comprehensive business continuity planning services. CorpInfoTech can help organizations, quantify, create, refine, and mitigate the risks presented by business threatening disasters in whatever form they may be disguised.