Fight The Phish!
October was cybersecurity awareness month which means it's your annual reminder to fight phishing in your workplace and at home. Social engineering is the easiest way hackers can break into your network. You could have all of the right security controls in place, but if a human makes a mistake or clicks the wrong link it may not be enough. Your workers need to learn how to fight phishing and avoid becoming a victim of social engineering.
What is Phishing?
Most people have some concept of what phishing is and how to avoid it, but as phishing evolves so must our knowledge of how to spot an attempt. Phishing refers to a method of social engineering where a bad actor will send an email, SMS message, or voice message to trick an individual into handing over valuable information such as login credentials or other private information your organization doesn't want in the wrong hands.
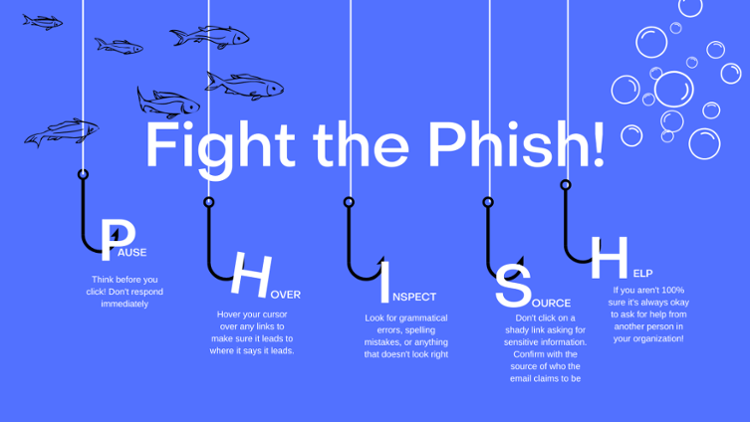
- Pause: Think before you click! Don't respond immediately to an email you think is out of the ordinary. Bad actors rely on you reacting off of emotion.
- Hover: Hover your cursor over any links to make sure it leads to where it says it leads.
- Inspect: Look for grammatical errors, spelling mistakes, or anything that doesn't look right.
- Source: If an email is asking you to click on a shady link, confirm with the source of who the email claims to be. If the message claims to be from your boss, double check to make sure it was really them who sent it.
- Help: If you aren't 100% sure in regards to the legitimacy of an email it's always okay to ask for help from another person in your organization!
Use all of these tactics to make sure that you are prepared from when a phishing scheme enters your inbox. Often times the weakest link in your organization are your humans who simply don't know how to respond. Learn to fight the phish and protect your organization!
CorpInfoTech (Corporate Information Technologies) provides small to mid-market organizations with expert I.T. services including compliance assessment, cybersecurity penetration tests, and comprehensive business continuity planning services. CorpInfoTech can help organizations, quantify, create, refine, and mitigate the risks presented by business threatening disasters in whatever form they may be disguised.



