NIST Recent Update: Simulated Social Engineering Testing
Simulating social engineering testing will allow your employees to make smarter security decisions, hopefully making your company more secure.
CorpInfoTech is honored to be partnered with KnowBe4. Together we will help secure your company from cyber criminals — Keeping You Informed and Aware. Below is a blog written by KnowBe4 . . .
Here is what Perry Carpenter, KnowBe4's Chief Evangelist and Strategy Officer had to say about NIST recent updates:
"If you’ve been in IT or infosec for any length of time, you’ve probably heard of NIST (the National Institute of Standards and Technology). In fact, the NIST 800 series is widely heralded as the de facto “go to” resource for guidance running most aspects of a security program... including security awareness training.
NIST recently updated Special Publication 800-53, Security and Privacy Controls for Information Systems and Organizations, adding some critical new language to the sections covering security awareness. Here’s the skinny. The relevant language is within Section 3.2 (see page 60).
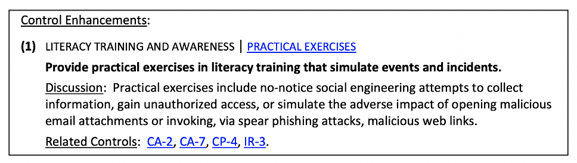
Notice that the updated NIST standard now includes providing frequent simulated social engineering testing. Specifically, their language states, “practical exercises include no-notice social engineering attempts to collect information, gain unauthorized access, or simulate the adverse impact of opening malicious email attachments or invoking, via spear phishing attacks, malicious web links.”
This is a significant addition from NIST and is a formal recognition that phishing simulation vendors, like KnowBe4, are providing a much-needed security control. This behavior-based training is the key to building an effective last line of defense. So, let’s examine their recommendation in detail.
- NIST’s recommendation is that security awareness testing be “no-notice.” This means that, while users may be aware of the fact that they should expect to be tested, they are not notified about the specifics of the test. In other words, there isn’t an announcement saying, “Hey! Be prepared for the phishing test this week!”.
- NIST is saying that the phishing tests should not be one-dimensional. It’s not just about being able to avoid clicking a link. They recommend testing to see if your people are vulnerable to credential harvesting attacks, downloading malicious attachments, enabling macros, and more.
- NIST adds that you should also include highly crafted spear phishing attacks. Any threat actor who is truly targeting your organization will take the time to do proper reconnaissance to build a potent attack. That’s what you are testing for. And that’s what NIST is recognizing here."
Carpenter continued: "In short, NIST is saying that your simulated social engineering testing needs to reflect real world threats so that you have a true understanding of your susceptibility to such threats.
"KnowBe4’s mission is to enable your employees to make smarter security decisions, every day. And we’ve been doing that for the past ten years through a combination of simulated social engineering testing, highly engaging content, and leading-edge automation. It is encouraging to see NIST’s formal recognition of the importance of simulated social engineering and we look forward to continuing to help our customers strengthen their last line of defense."
CorpInfoTech is here and ready for social engineering testing with your company — don’t let your humans be the weakest link.
Corporate Information Technologies provides small to mid-market organizations with expert I.T. services including compliance assessment, cybersecurity penetration tests, and comprehensive business continuity planning services. Corporate Information Technologies can help organizations, quantify, create, refine, and mitigate the risks presented by business threatening disasters in whatever form they may be disguised.




