A Brief Overview of HIPAA Compliance
A Brief Overview of HIPAA
As an organization you may be in charge of storing and exchanging client information across your network daily. Whether you provide financial services, healthcare services, real estate, etc you most likely are in charge of protecting someone else's personal data. While storing such information digitally is convenient, it does come with risks that need to be addressed in order to maintain a trustworthy and secure relationship between you and your clients. To ensure that security most organizations will have to comply with rules and regulations on how data is stored and protected. One such set of regulations is known as HIPAA or " The Health Insurance Portability and Accountability Act". Read on to learn more about what HIPAA is and whether or not it applies to you.
What is HIPAA?
As previously mentioned HIPAA is a set of regulations that assist in protecting sensitive, personal data. Specifically, HIPAA applies to the healthcare field and is concerned with "protected health information" (PHI). Examples of PHI include: names, addresses, social security numbers, medical records, health plan beneficiary numbers, as well as dozens of other forms of data including anything with a unique ID number or code. If you are a healthcare provider, healthcare clearinghouse, or in charge of maintaining health plans then you are required by federal law to comply with HIPAA. Additionally, if you are a business associate with any of these entities then you are also required to abide by certain HIPAA regulations. Any entity that is found to be non compliant will face financial and potential legal repercussions.
Now more than ever it is important to make sure that your organization is compliant with HIPAA. Through the COVID-19 pandemic we have seen that healthcare providers have become a sizable target for cyber criminals in the past two years. With the influx of patients comes a larger attack surface that the healthcare field will have to manage for years to come.
The Scope of HIPAA
The framework of HIPAA is a complex one that contains roughly 50 implementation standards that organizations must be aware of. While most of those standards are outside the scope of this piece it is important to understand the general framework of HIPAA.
HIPAA is broken down into 5 "titles" that each cover an aspect of the overall standard and within these titles are rules and regulations that aid in securing patient information. However, when people refer to HIPAA they are most often referring to Title II or "Administrative Simplification".
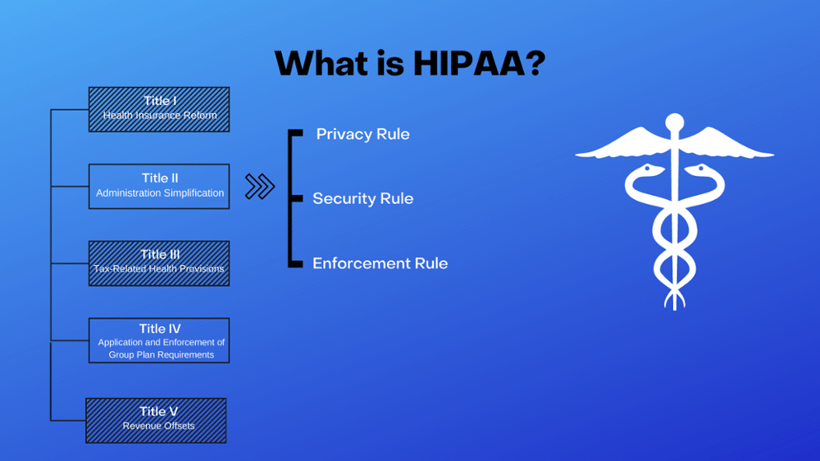
Title II establishes a national standard for how electronic healthcare transactions are processed and secured. It is primarily concerned with making sure access to PHI is both available and secure. To do this there are a few rules within title II that entities must comply to.
Privacy Rule
The standards for Privacy of Individually Identifiable Health Information, or the HIPPA Privacy rule establishes a set of standards for how healthcare providers are to protect patient health information. This rule includes enacting sets of policies to ensure privacy of PHI as well as appointing personnel to implement and develop said policies. In addition to this the privacy rule also outlines what it looks like for organizations to train their employees, mitigate violations, document and record ( at least six years), and establish avenues in which patients can file grievances with privacy compliance's.
Security Rule
The HIPAA security rule creates guidelines for how entities safeguard electronic health records (EHR) to make sure that patient data is safe and secure. There are three broad types of protection that the security rule provides: Technical safeguards, Physical safeguards, Administrative safeguards.
Technical safeguards include access controls, transmission security, auditing, and entity authentication. Having systems in place to identify threats and maintain security through various controls and authentication protocols will aid in making sure that data is safe.
Physical safeguards refer to protecting the actual hardware and physical tech from being breached. This means that access to workstations and other devices should be monitored and secured from attackers or unauthorized personnel.
Lastly, administrative safeguards implement recovery plans, security awareness training, data breach procedures, etc. While putting up firewalls and forcing 2FA can be effective in protecting an organization from a cyber attack, it is equally as important to educate employees on how to avoid and respond to potential threats.
Breach Notification Rule
The breach notification rule makes sure that any and all HIPAA violations are notified to certain groups. This includes notifying individuals who's PHI may have been compromised in a breach, making some sort of media announcement if said breach impacts more than 500 people, as well as notifying the proper officials inside and out of your organization. This makes ensures that if PHI is stolen the applicable person is notified and that the organization is engaging in remediation efforts.
How Does This Impact Your Business?
While these rules don't encompass all of HIPAA it is important to have a basic understanding of what it seeks to do as well as who it applies to. If you believe your organization to be one of the entities required to comply with HIPAA regulations then you can contact CorpInfoTech today to learn how you can be assessed and compliant. We can asses your security posture and identify where you are lacking in compliance. Additionally, if you would like to learn more about the Health Insurance Portability and Accountability Act reach out to us!
CorpInfoTech (Corporate Information Technologies) provides small to mid-market organizations with expert I.T. services including compliance assessment, cybersecurity penetration tests, and comprehensive business continuity planning services. CorpInfoTech can help organizations, quantify, create, refine, and mitigate the risks presented by business threatening disasters in whatever form they may be disguised.




